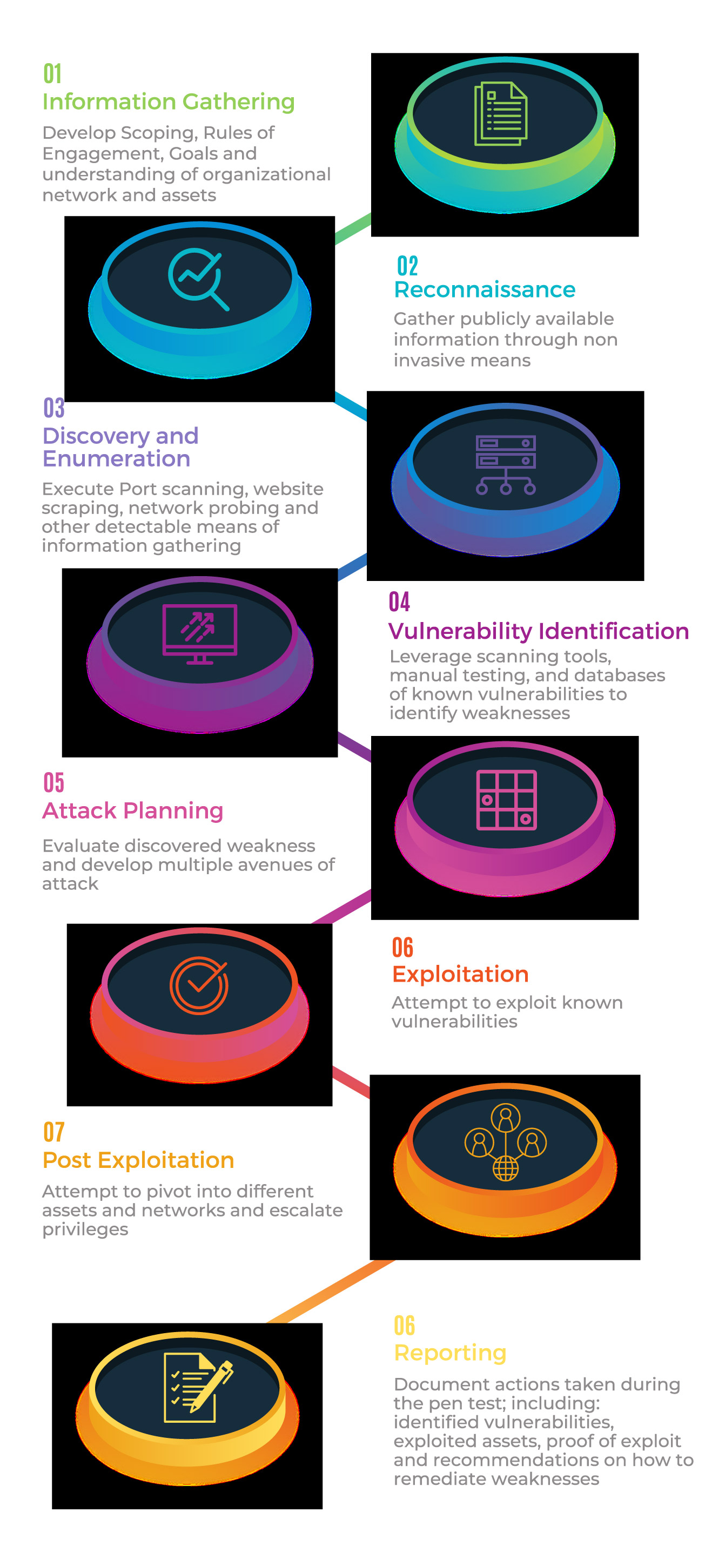
About Penetration Testing
Proactively protect your assets and your data. Penetration Testing identifies vectors of attack and vulnerabilities before attackers do allow you to uncover critical issues before they are exploited. Pen Testing leverages real-world attack vectors and scenarios to attempt to exploit known, unknown and suspected vulnerabilities. All Penetration Testing lays out the boundaries, methodology and rules of engagement for the engagement. GAI Cyber has a numerous OSCPs and OSCEs on staff that have in-depth expertise in various functional technology domains, including: web server, mobile device, application, database, wireless, APIs, network, physical security, and social engineering. The GAI Cyber Penetration Testing team offers internal, external, white box, gray box and black box testing and leverages a methodical approach to each engagement.
Why GAI Cyber Solutions
GAI Compliance Solutions.
Vulnerability Scanning
Identify. Investigate. Remediate.