SOC2 Compliance
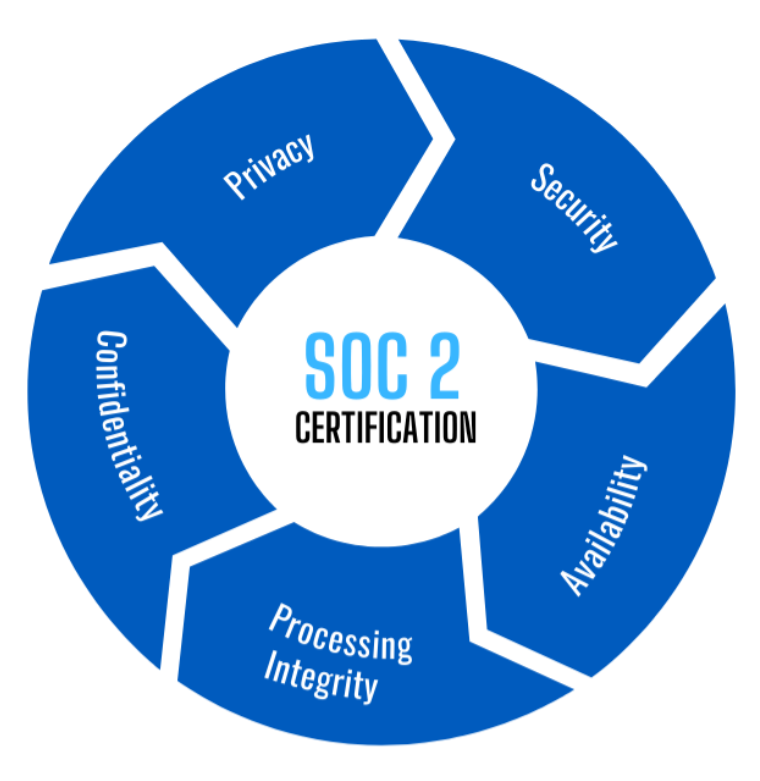
SOC 2 is a voluntary compliance standard that was developed by the American Institute of CPAs (AICPA). The standard is based on the following Trust Services Criteria: security, availability, processing integrity, confidentiality, privacy.
SOC 2 Focuses on a service organization’s controls related to: security, availability, processing integrity of a system, and the confidentiality of the information processed by a system.
Other types of SOC Compliance include:
SOC 1
Focuses on business and financial controls and reporting of a service organization.
SOC 3
A redacted version of a SOC 2 report. Removes proprietary and/or confidential information so that the report can be made public.
SOC for Cybersecurity
Focuses on an entity’s cybersecurity risk management program; meant for investors, boards of directors, and senior management.
SOC for Supply Chain
A report to help entities better assess and manage supply chain risk. Provides an audited track record for customers, business partners, and other interested parties to show a commitment by the entity to these stakeholders.
Some of the reasons organization choose to pursue SOC 2 certification, include:
Demonstrating compliance with an agnostic and recognized security standard
Leveraging successful SOC 2 reports to meet vendor and partner security requirements and surveys
Why GAI Cyber Solutions
GAI Compliance Solutions.
Vulnerability Scanning
Identify. Investigate. Remediate.